You are here: Home1 / DoD Workforce Innovation Directorate2 / DoD Cyber Workforce Framework3 / DCWF Training
DCWF Training
DCWF Orientation
DoD Cyber Workforce Framework (DCWF) Orientation is an eLearning course designed to familiarize learners with the fundamental principles of the DCWF. This course an introduction to the policies and key attributes of the DCWF, and it outlines why the DCWF is critical to organizing and consolidating different positions as Work Roles across the DoD.
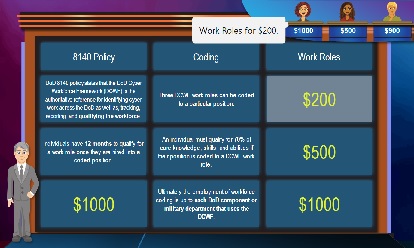
Game Show: DCWF Edition!
Whether you’re supplementing your training in DCWF Orientation or coming back for a refresher, this learning game is designed to test your knowledge of the Defense Cyber Workforce Framework (DCWF). Play against 2 other virtual contestants who will try to beat you. Score cash prizes. See how your knowledge stacks up in Game Show: DCWF edition!